Western Carolina University (20)
View all
- Canton Champion Fibre Company (2308)
- Cherokee Traditions (293)
- Civil War in Southern Appalachia (165)
- Craft Revival (1942)
- Great Smoky Mountains - A Park for America (2767)
- Highlights from Western Carolina University (430)
- Horace Kephart (941)
- Journeys Through Jackson (154)
- LGBTQIA+ Archive of Jackson County (26)
- Oral Histories of Western North Carolina (314)
- Picturing Appalachia (6772)
- Stories of Mountain Folk (413)
- Travel Western North Carolina (160)
- Western Carolina University Fine Art Museum Vitreograph Collection (129)
- Western Carolina University Herbarium (92)
- Western Carolina University: Making Memories (708)
- Western Carolina University Publications (2283)
- Western Carolina University Restricted Electronic Theses and Dissertations (146)
- Western North Carolina Regional Maps (71)
- World War II in Southern Appalachia (131)
University of North Carolina Asheville (6)
View all
- Allanstand Cottage Industries (62)
- Appalachian National Park Association (53)
- Bennett, Kelly, 1890-1974 (1388)
- Berry, Walter (76)
- Brasstown Carvers (40)
- Carver, George Washington, 1864?-1943 (26)
- Cathey, Joseph, 1803-1874 (1)
- Champion Fibre Company (233)
- Champion Paper and Fibre Company (297)
- Cherokee Indian Fair Association (16)
- Cherokee Language Program (22)
- Crowe, Amanda (40)
- Edmonston, Thomas Benton, 1842-1907 (7)
- Ensley, A. L. (Abraham Lincoln), 1865-1948 (275)
- Fromer, Irving Rhodes, 1913-1994 (70)
- George Butz (BFS 1907) (46)
- Goodrich, Frances Louisa (120)
- Grant, George Alexander, 1891-1964 (96)
- Heard, Marian Gladys (60)
- Kephart, Calvin, 1883-1969 (15)
- Kephart, Horace, 1862-1931 (313)
- Kephart, Laura, 1862-1954 (39)
- Laney, Gideon Thomas, 1889-1976 (439)
- Masa, George, 1881-1933 (61)
- McElhinney, William Julian, 1896-1953 (44)
- Niggli, Josephina, 1910-1983 (10)
- North Carolina Park Commission (105)
- Osborne, Kezia Stradley (9)
- Owens, Samuel Robert, 1918-1995 (11)
- Penland Weavers and Potters (36)
- Roberts, Vivienne (15)
- Roth, Albert, 1890-1974 (142)
- Schenck, Carl Alwin, 1868-1955 (1)
- Sherrill's Photography Studio (2565)
- Southern Highland Handicraft Guild (127)
- Southern Highlanders, Inc. (71)
- Stalcup, Jesse Bryson (46)
- Stearns, I. K. (213)
- Thompson, James Edward, 1880-1976 (226)
- United States. Indian Arts and Crafts Board (130)
- USFS (683)
- Vance, Zebulon Baird, 1830-1894 (1)
- Weaver, Zebulon, 1872-1948 (58)
- Western Carolina College (230)
- Western Carolina Teachers College (282)
- Western Carolina University (1794)
- Western Carolina University. Mountain Heritage Center (18)
- Whitman, Walt, 1819-1892 (10)
- Wilburn, Hiram Coleman, 1880-1967 (73)
- Williams, Isadora (3)
- Cain, Doreyl Ammons (0)
- Crittenden, Lorraine (0)
- Rhodes, Judy (0)
- Smith, Edward Clark (0)
- Appalachian Region, Southern (2399)
- Asheville (N.C.) (1917)
- Avery County (N.C.) (26)
- Blount County (Tenn.) (161)
- Buncombe County (N.C.) (1671)
- Cherokee County (N.C.) (283)
- Clay County (N.C.) (555)
- Graham County (N.C.) (233)
- Great Smoky Mountains National Park (N.C. and Tenn.) (510)
- Haywood County (N.C.) (3522)
- Henderson County (N.C.) (70)
- Jackson County (N.C.) (4692)
- Knox County (Tenn.) (25)
- Knoxville (Tenn.) (12)
- Lake Santeetlah (N.C.) (10)
- Macon County (N.C.) (420)
- Madison County (N.C.) (211)
- McDowell County (N.C.) (39)
- Mitchell County (N.C.) (132)
- Polk County (N.C.) (35)
- Qualla Boundary (981)
- Rutherford County (N.C.) (76)
- Swain County (N.C.) (2113)
- Transylvania County (N.C.) (247)
- Watauga County (N.C.) (12)
- Waynesville (N.C.) (73)
- Yancey County (N.C.) (72)
- Aerial Photographs (3)
- Aerial Views (60)
- Albums (books) (4)
- Articles (1)
- Artifacts (object Genre) (228)
- Bibliographies (1)
- Biography (general Genre) (2)
- Cards (information Artifacts) (38)
- Clippings (information Artifacts) (191)
- Crafts (art Genres) (622)
- Depictions (visual Works) (21)
- Design Drawings (1)
- Drawings (visual Works) (184)
- Envelopes (73)
- Facsimiles (reproductions) (1)
- Fiction (general Genre) (4)
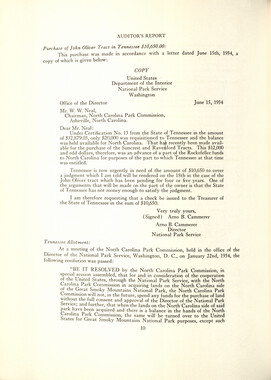
- Financial Records (12)
- Fliers (printed Matter) (67)
- Glass Plate Negatives (381)
- Guidebooks (2)
- Internegatives (10)
- Interviews (812)
- Land Surveys (102)
- Letters (correspondence) (1013)
- Manuscripts (documents) (619)
- Maps (documents) (177)
- Memorandums (25)
- Minutes (administrative Records) (59)
- Negatives (photographs) (5835)
- Newsletters (1285)
- Newspapers (2)
- Occupation Currency (1)
- Paintings (visual Works) (1)
- Pen And Ink Drawings (1)
- Periodicals (193)
- Personal Narratives (10)
- Photographs (12976)
- Plans (maps) (1)
- Poetry (7)
- Portraits (1960)
- Postcards (329)
- Programs (documents) (151)
- Publications (documents) (2237)
- Questionnaires (65)
- Scrapbooks (282)
- Sheet Music (2)
- Slides (photographs) (402)
- Songs (musical Compositions) (2)
- Sound Recordings (796)
- Specimens (92)
- Speeches (documents) (15)
- Tintypes (photographs) (8)
- Transcripts (322)
- Video Recordings (physical Artifacts) (23)
- Vitreographs (129)
- Text Messages (0)
- A.L. Ensley Collection (275)
- Appalachian Industrial School Records (7)
- Appalachian National Park Association Records (336)
- Axley-Meroney Collection (2)
- Bayard Wootten Photograph Collection (20)
- Bethel Rural Community Organization Collection (7)
- Blumer Collection (5)
- C.W. Slagle Collection (20)
- Canton Area Historical Museum (2110)
- Carlos C. Campbell Collection (282)
- Cataloochee History Project (65)
- Cherokee Studies Collection (4)
- Daisy Dame Photograph Album (5)
- Daniel Boone VI Collection (1)
- Doris Ulmann Photograph Collection (112)
- Elizabeth H. Lasley Collection (1)
- Elizabeth Woolworth Szold Fleharty Collection (4)
- Frank Fry Collection (95)
- George Masa Collection (173)
- Gideon Laney Collection (452)
- Hazel Scarborough Collection (2)
- Hiram C. Wilburn Papers (28)
- Historic Photographs Collection (236)
- Horace Kephart Collection (861)
- Humbard Collection (33)
- Hunter and Weaver Families Collection (1)
- I. D. Blumenthal Collection (4)
- Isadora Williams Collection (4)
- Jesse Bryson Stalcup Collection (47)
- Jim Thompson Collection (224)
- John B. Battle Collection (7)
- John C. Campbell Folk School Records (80)
- John Parris Collection (6)
- Judaculla Rock project (2)
- Kelly Bennett Collection (1407)
- Love Family Papers (11)
- Major Wiley Parris Civil War Letters (3)
- Map Collection (12)
- McFee-Misemer Civil War Letters (34)
- Mountain Heritage Center Collection (4)
- Norburn - Robertson - Thomson Families Collection (44)
- Pauline Hood Collection (7)
- Pre-Guild Collection (2)
- Qualla Arts and Crafts Mutual Collection (12)
- R.A. Romanes Collection (681)
- Rosser H. Taylor Collection (1)
- Samuel Robert Owens Collection (94)
- Sara Madison Collection (144)
- Sherrill Studio Photo Collection (2558)
- Smoky Mountains Hiking Club Collection (616)
- Stories of Mountain Folk - Radio Programs (374)
- The Reporter, Western Carolina University (510)
- Venoy and Elizabeth Reed Collection (16)
- WCU Gender and Sexuality Oral History Project (32)
- WCU Mountain Heritage Center Oral Histories (25)
- WCU Oral History Collection - Mountain People, Mountain Lives (71)
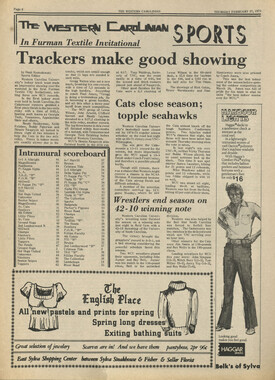
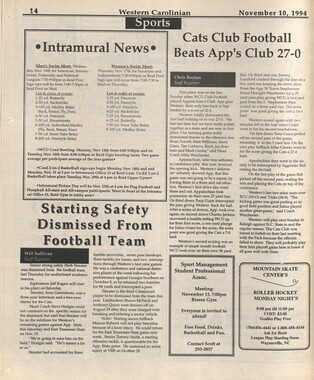
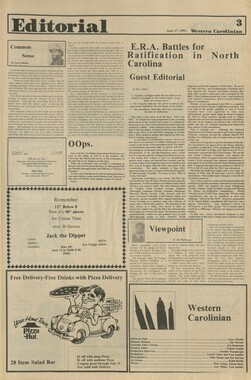
- WCU Students Newspapers Collection (1744)
- Western North Carolina Tomorrow Black Oral History Project (69)
- William Williams Stringfield Collection (2)
- Zebulon Weaver Collection (109)
- African Americans (390)
- Appalachian Trail (35)
- Artisans (521)
- Cherokee art (84)
- Cherokee artists -- North Carolina (10)
- Cherokee language (21)
- Cherokee pottery (101)
- Cherokee women (208)
- Church buildings (167)
- Civilian Conservation Corps (U.S.) (110)
- College student newspapers and periodicals (1830)
- Dams (103)
- Dance (1023)
- Education (222)
- Floods (61)
- Folk music (1015)
- Forced removal, 1813-1903 (2)
- Forest conservation (220)
- Forests and forestry (1058)
- Gender nonconformity (4)
- Great Smoky Mountains National Park (N.C. and Tenn.) (181)
- Hunting (38)
- Landscape photography (10)
- Logging (103)
- Maps (84)
- Mines and mineral resources (8)
- North Carolina -- Maps (18)
- Paper industry (38)
- Postcards (255)
- Pottery (135)
- Railroad trains (71)
- Rural electrification -- North Carolina, Western (3)
- School integration -- Southern States (2)
- Segregation -- North Carolina, Western (5)
- Slavery (5)
- Sports (452)
- Storytelling (245)
- Waterfalls -- Great Smoky Mountains (N.C. and Tenn.) (66)
- Weaving -- Appalachian Region, Southern (280)
- Wood-carving -- Appalachian Region, Southern (328)
- World War, 1939-1945 (173)
Western Carolinian Volume 67 Number 08
Item
Item’s are ‘child’ level descriptions to ‘parent’ objects, (e.g. one page of a whole book).
-
-
september 18-24, 2002 technolo 0 news ewsma azine TECHNOLOGY NEWS "Microsoft Update"? HIMOWITZ ON COMPUTERS: Windows— More Roles Than a Prairie Dog Colony By Michael J. Him owitz - The Baltimore Sun 4} t's almost like a greeting from an old friend. You start up your computer, log on to the Internet, and up pops a little gray box: "Microsoft Critical Update Notification: New critical updates are available for your computer. Microsoft strongly suggests that you install these updates now. " When you click the "View Updates" button, you're whisked to Microsoft's Web site, where you can download a fix for the latest Windows security flub. I've seen plenty of these warnings lately. Last week, it was a fix for a critical security flaw that threatened my "Digital Certificates," whatever they are. The week before it was yet another security bug in Internet Explorer that could allow a hacker to take over my computer, and before that, a flaw in Office XP that could allow a script kiddie in Kazakhstan to burn down my house by remote control, or something like that. All told, Microsoft has issued 48 security bulletins so far this year, and may well break last year's record of 60. That doesn't count security bugs that other people discover and make public before Microsoft gets a chance to announce them. What's going on here? Are we risking life, liberty and property every time we turn on our computers? The answer is no. And yes. There's no question that Microsoft Windows and its primary applications have more holes than a prairie dog colony. This is the legacy of a corporate culture that developed around personal computers in the 1980s, when few PCs were connected to anything. The young Bill Gates and his Microsoft cohorts were hackers of the old school whose mission in life was to make computers do cool things and provide tools for developers and users who wanted to do the same thing. The notion that somebody might use those same tools to create mischief wasn't on anybody's mind. Fast forward 20 years and we have hundreds of millions of PCs that are connected on corporate networks and over the Internet. Unfortunately, those computers run software that was the product of a stand-alone mind-set. Consider Internet Explorer and its companion e-mail programs, Outlook and Outlook Express. A Web browser by definition is a programming tool that allows an intruder to take control of your computer—albeit at your invitation. In the best of all worlds, a browser should put strict limits on what a Web programmer can do. It certainly shouldn't let the Web page designer steal information, destroy files or plant programs that can take over your computer. Although it never deliberately let that happen, Microsoft expended far more effort on adding new features and e-commerce tools to IE than it did on building defenses against hackers who might turn those features around for nefarious purposes. Over the past few years, hackers have figured out how to do just that. Outlook and Outlook Express compound these security flaws when you display e- mail in Web page format. No longer do you have to visit a Web site to execute malicious code. All you have to do is open your mail or browse through it in a preview window. Moreover, because Microsoft has built so many programming "hooks" into Windows, it's relatively easy for virus writers to hijack Outlook to spread their work around the world. Unfortunately, these are just two of the many security lapses that Microsoft has been hammered for over the past two years. Many others affect the servers that run corporate networks, e-commerce operations and Web sites. Gates finally owned up to the problem in January, when he sent a rare message to all Microsoft employees announcing a new "Trustworthy Computing" initiative. Henceforth, he declared, the company's top priority would be security and user privacy—new programs and features would come second. Indeed, Microsoft is cleaning up its act. When it finds a flaw, it generally fixes the problem, announces it to the world and—if the bug is serious enough—invites users to download a fix. Which raises another question. How serious are these security bugs? They're certainly treated seriously in the press when Microsoft itself calls them "critical. " Since I've never been bitten by one, I called the best professional troubleshooter I know, Marc Seidler, and asked him how often he encounters the problems these fixes are designed to prevent. Seidler, proprietor of a local consulting business known as The Computer Doctors, has operated on thousands of troubled PCs in businesses and homes over the past half-dozen years. He regularly monitors Microsoft's technical Web sites, which he says are excellent. "I have never seen one of these sort of security issues" in a client's computer, he said. "Most of these things are discovered in the lab," he added, and many are important mainly to large businesses with sophisticated networks. "But if you're sitting at home and have Comcast or DSL (Internet service), it's not an issue. The latest "critical" announcement is a case in point. It describes scenario in which a malicious Web page could execute obscure code that deletes Digital Certificates from a user's computer. These are files containing the keys that allow users to encrypt e-mail (which almost no one does) and more importantly, exchange credit card and other information securely and transparently with e-commerce Web sites. As it turns out, no one has actually done this. In fact, Microsoft discovered the flaw during a routine internal security audit. So why a "critical" update? Because under Microsoft's standards (clearly spelled out on its security Web site), a critical problem is one that could result in code being executed on a user's computer without the user's intervention. The critical designation has nothing to do with the likelihood of an attack. In fact, many of the company's security updates describe flaws that have been found by Microsoft employees or security companies who spend their time probing for cracks in the wall. Seidler says viruses pose a far more serious threat to most users and recommends installing a virus checker and keeping it up to date. Does this mean you shouldn't pay attention when you get a "critical" update notification? Of course you should. Just realize that the flaws you read about so frequently don't signal the end of computing as we know it. For the latest Microsoft security bulletins, surf to www.microsoft.com/technet/ and click on Security in the main menu. Distributed by the Los Angeles Times-Washington Post News Service 02002 The Baltimore Sun TECHNOLOGY NEWS - cyber Security Legislation Administration Pares Down Cyber-security Plan By Ariana Eunjung Cha I The Washington Post As the White House moves to finalize a national plan to better secure cyberspace, high- tech firms and other companies are continuing a furious campaign to have some recommendations struck from the document. The administration no longer plans to recommend that Internet service providers such as America Online, MSN and EarthLink bundle firewall and other security technology with their software. Instead, it will ask ISPs to "make it easier" for home users to get access to such protections. It also does not plan to recommend that a privacy czar be appointed to oversee how companies make use of their customers' personal information, according to several people involved in drafting the document. A government official said the changes were made in hopes the plan would be adopted voluntarily by industry and not necessitate another layer of government regulation. Several companies have argued that if the government tells people what to buy and dictates how they should run their businesses, innovation will be squelched. But others said private industry was more concerned about the costs involved in carrying out the recommendations. Businesses also worry about taking on new legal liability. "I've been really shocked at how companies have been acting in their own interest rather than in the national interest," said Allan Paller, director of the SANS Institute, a computer- security think tank and education center. Harris Miller, president of the Information Technology Association of America, which represents 500 companies, said the private sector is in no way trying to dilute the plan. It was the industry, in fact, that first suggested a plan be developed, he said. "The idea that industry is somehow a reluctant partner is inaccurate," Miller said. At about 150 pages, the National Strategy to Secure Cyberspace, which is scheduled to be released Sept. 18, remains a weighty document outlining about 80 new obligations for the government, companies, universities and even home computer users. The most extensive recommendations are for the government. The plan would restrict federal workers from using certain wireless technologies and mandate that agencies only purchase software that has been certified to be secure. One of the top priorities, according to one draft, is for the government and the private sector is to make sure computers that control major systems such as subways, nuclear reactors and dams are secure. Also under consideration are recommendations calling for the establishment of a center that would study computer viruses, worms and other security threats; an accreditation board that would certify security personnel; and a private-public program that would help pay for security enhancements for critical parts of the Internet, including the routers that direct traffic, as well as operating systems such as Windows, Linux and the Mac OS. Some drafts also outline plans for the collection and analysis of network data that pass through universities _ places often used as jumping-off points for cyber-attacks. The draft also includes a plan to educate home users on how to secure their computers. The national strategy is being compiled and analyzed by Richard Clarke, director of the Office of Cyberspace Security, with input from a cross section of industry representatives, computer science experts and others. It is scheduled to be delivered to President Bush for his signature in the next week. 02002 THE WASHINGTON POST
Object
Object’s are ‘parent’ level descriptions to ‘children’ items, (e.g. a book with pages).
-
The Western Carolinian is Western Carolina University's student-run newspaper. The paper was published as the Cullowhee Yodel from 1924 to 1931 before changing its name to The Western Carolinian in 1933.
-